NIST Cybersecurity Framework 2.0. Operating System
As Cloud Services revolutionized the creation and management of digital infrastructure, the DVMS Institute CPD Overlay Model, underpinned by the NIST Cybersecurity Framework and its informative references, will revolutionize how organizations manage their digital risk, resiliency, and privacy.
The landscape of digital outcomes has rapidly evolved, as have the accompanying threats and challenges. The DVMS Institute recognizes these challenges and is committed to reshaping how organizations perceive and manage digital risk, resiliency, and privacy.
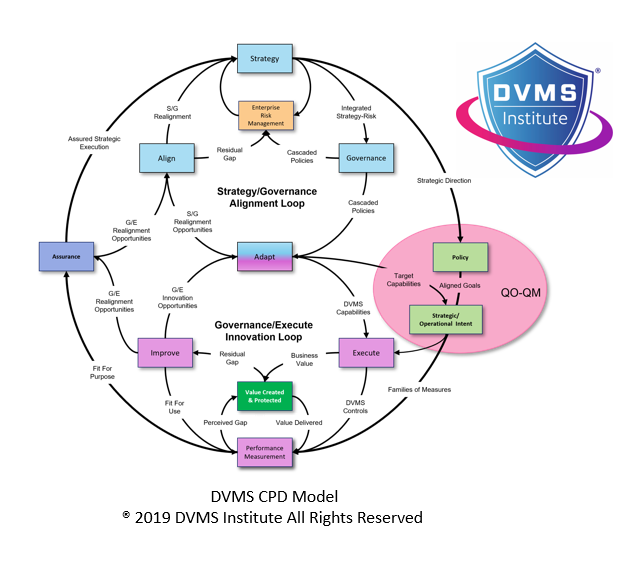
The DVMS Institute’s Mission is to provide organizations with a NIST Cybersecurity Framework 2.0. operating system that facilitates secure, resilient, and auditable digital outcomes. To do this, the Institute has created a CPD overlay operating system capable of providing organizations of any size, scale, or complexity with a simple, practical, and scalable way to operationalize the NIST-CSF seven-step model.
The institute’s Vision is to serve as that guiding light by teaching organizations of any size, scale, or complexity how to create a digital value overlay system capable of meeting the stringent expectations of both government regulators and operational stakeholders.
NIST Cybersecurity Framework /DVMS-CPD Seven-Step Model
Step 1: Prioritize and Scope.
The organization identifies its business/mission objectives and high-level organizational priorities with risk tolerances expressed in a target Implementation Tier.
The CPD Strategy/Governance Alignment Loop identifies and operationalizes business/mission objectives and high-level organizational priorities. The organization expresses its business objectives through strategic direction and integrated strategy-risk governance policies. Those policies are inclusive of current and future state risk tolerances.
Step 2: Orient.
The organization identifies related systems and assets, regulatory requirements, and overall risk approach and then consults sources to identify threats and vulnerabilities applicable to those systems and assets.
The CPD Model Strategy-Risk policies identify related systems and assets, regulatory requirements, and the overall risk approach. Enterprise Risk Management (ERM) provides the relevant cyber risk input to develop the general strategic direction and strategy-risk policies. Identifying threats and vulnerabilities occurs within the Governance/Innovation loop, guided by the strategy-risk policies.
Step 3: Create a Current Profile.
The organization develops its current profile by documenting which Category and Subcategory outcomes from the Framework Core exist.
Assessing the current state enables organizations to establish their existing Framework profile. This baseline assessment is the starting point for organizations to innovate incrementally to sustain within their context. Note that the “current profile” describes verifiable and quantitative outcomes.
Step 4: Conduct a Risk Assessment.
This assessment is guided by the overall risk management process or previous risk assessment activities.
The CPD Model applies the risk assessment of the target profile using previous risk assessments and changes to organizational internal, external, and threat landscape needs. The CPD Model embodies two feedback loops that enable the organization to realign strategies or policies to improve or sustain cybersecurity operational capabilities.
Step 5: Create a Target Profile.
The organization creates a Target Profile that assesses the Framework Categories and Subcategories that describe the desired organizational cybersecurity outcomes.
The CPD Model supports the planning, design, change, and execution of the target state. In doing so, it considers all interactions and dependencies for existing capabilities.
Step 6: Determine, Analyze, and Prioritize Gaps.
The organization compares the Current Profile and the Target Profile to determine gaps. Next, it creates a prioritized action plan to address gaps that reflect mission drivers, costs and benefits, and risks to achieve the outcomes in the Target Profile.
In the CPD Model, this step occurs in the Governance/Execution & Innovation Loop. The detailed planning and design consider the scope of change to any dependent organizational capability and the modifications required to close cybersecurity performance gaps. In addition, planning and design include the instrumentation of the modified capabilities to gather appropriate metrics to ensure it is fit for use and auditable for purpose.
Step 7: Implement Action Plan.
The organization determines which actions to take to address the gaps identified in the previous step and then adjusts its current cybersecurity practices to achieve the Target Profile consistent with the requirements of the selected cybersecurity Informative References.
The CPD Model operationalizes gap mitigation through its change, execution, and innovation capabilities. The Governance/Execute & Innovation Loop adapts the new capabilities as identified, planned, designed, and built.
Conclusion
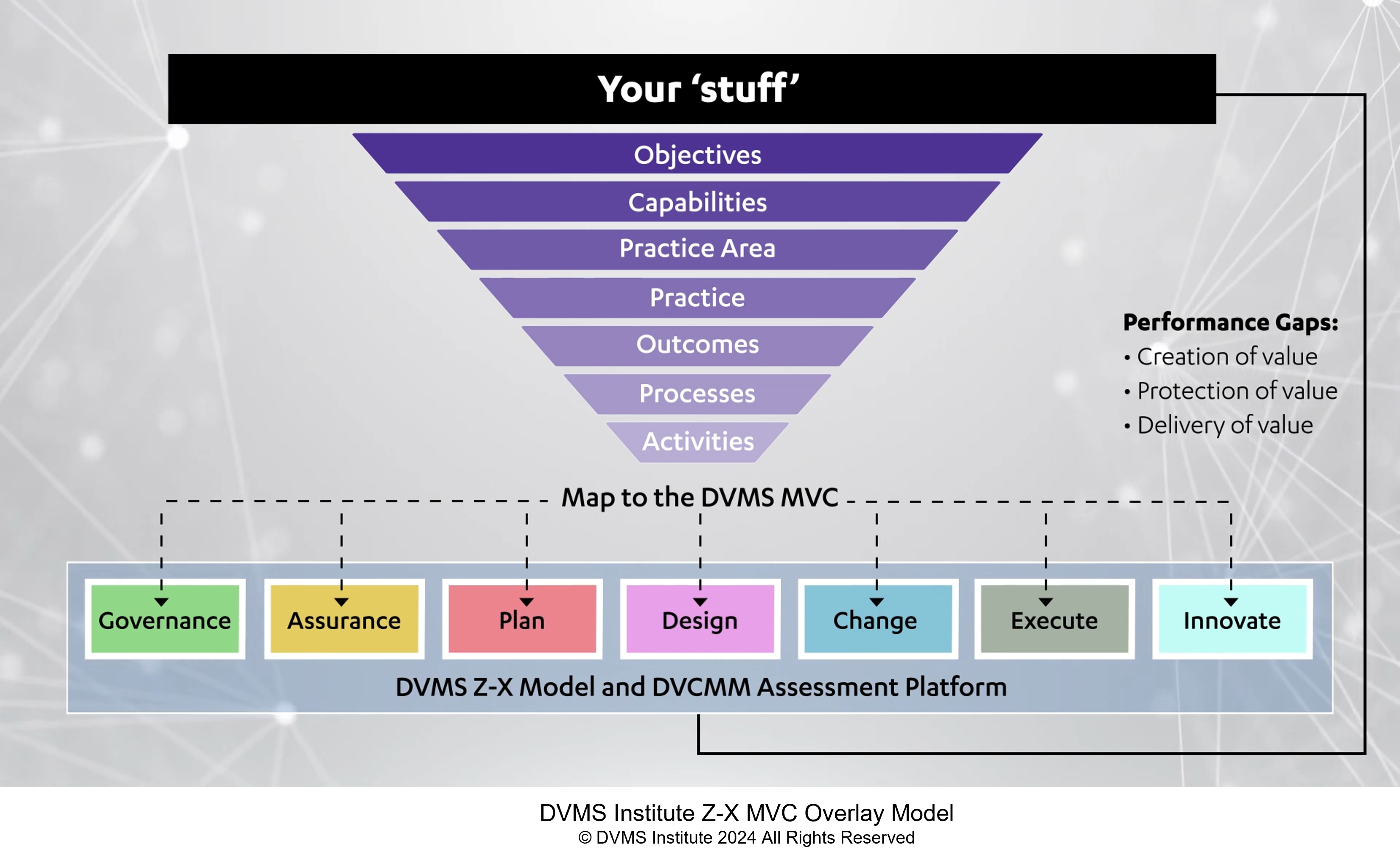
The DVMS Overlay Model enables organizations of any size, scale, and complexity to leverage existing business capabilities and well-known frameworks and standards (NIST, ISO, ITSM, GRC) to facilitate the delivery of secure, resilient, and auditable digital outcomes.
The following explainer videos will guide you through the specific facets of our comprehensive digital value management system (DVMS™) approach.
Institute Introduction:
The Institute’s introduction video encapsulates the Institute’s core philosophy. It’s not just about technology; it’s about culture. We advocate for a culture where digital business value creation, protection, and delivery are paramount.
The DVMS Overlay Model
This video is a deep dive into how we operationalize universally recognized frameworks like NIST and ISO. We believe that a one-size-fits-all solution is often not the answer. Tailoring frameworks to specific needs ensures both security and auditability.
How an Overlay Model Works
The overlay model provides organizations a scalable and cost-effective way to leverage existing business capabilities and resources to facilitate secure, resilient, and auditable digital business outcomes.
The DVMS CPD™ Model:
Layer upon layer, the digital enterprise is a complex web of operations. The CPD Model breaks down this complexity, ensuring each layer remains secure, resilient, and audit-ready.
The DVMS Z-X™ Model
The ZX Model is the embodiment of comprehensive planning. From inception to execution, every stage is designed to innovate and support the delivery of secure digital outcomes. It’s a roadmap for organizations to follow.
The DVMS 3D Knowledge™ Model:
Digital outcomes aren’t achieved in isolation. The 3D Knowledge Model fosters communication and collaboration, ensuring that every cog in the organizational machinery works harmoniously by understanding everyone’s role and dependencies in delivering secure digital outcomes.
The DVMS FastTrack™ Model:
Our Fast-Track Model serves as a guide for those keen on a phased, systematic adoption of these frameworks. It emphasizes pace, ensuring digital security and resilience without overwhelming adaptation.