SEC Rules and the NIST Cybersecurity Framework Digital Value Management System – A Synergistic Approach to SEC Compliance
Rick Lemieux – Co-Founder and Chief Product Officer of the DVMS Institute
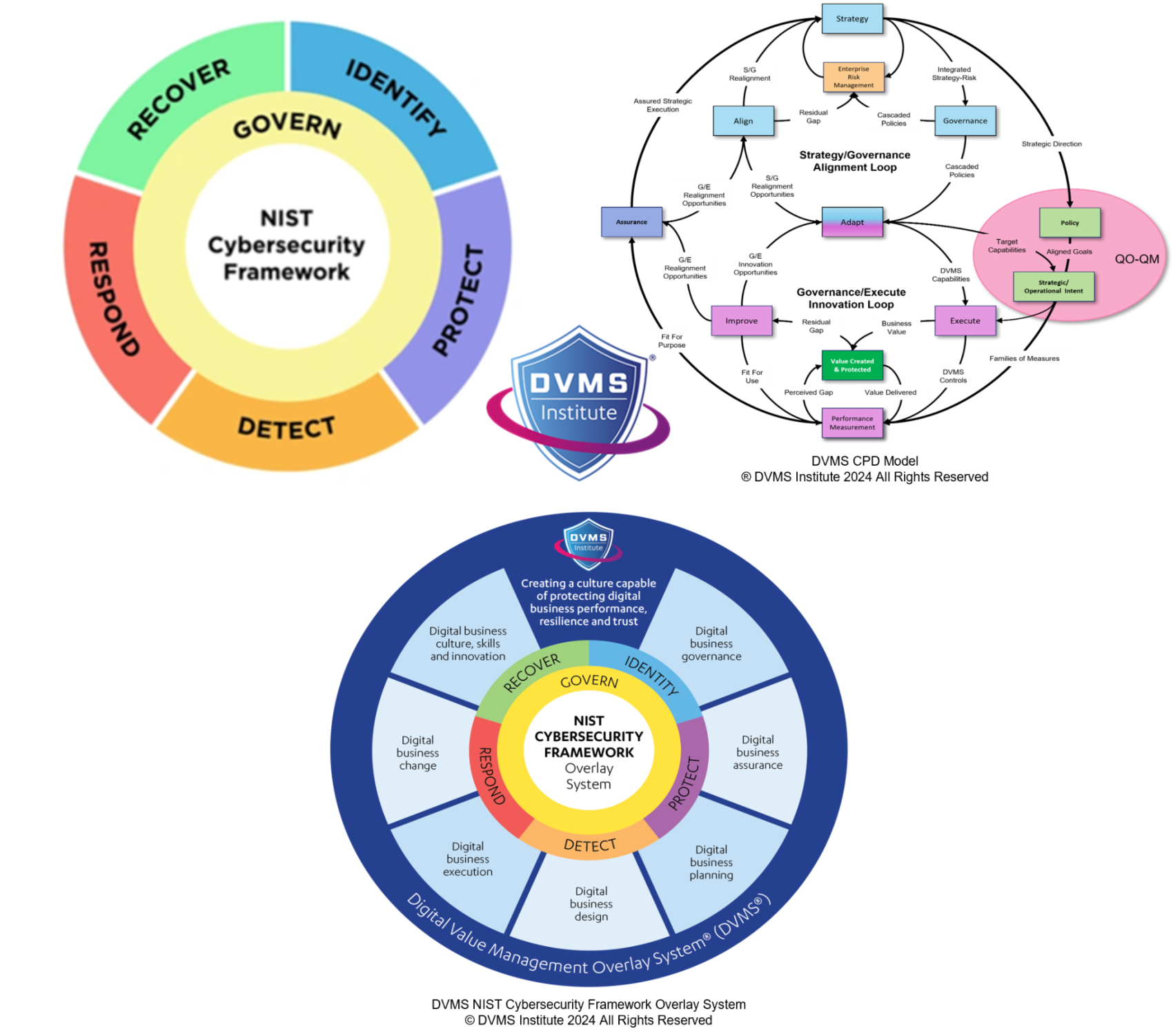
The Digital Value Management System™ (DVMS) provides a comprehensive and adaptable overlay system that aligns seamlessly with the U.S. Securities and Exchange Commission’s (SEC) Rules on Cybersecurity Risk Management, Strategy, Governance, and Incident Disclosure. These rules, which apply to all public companies registered under the Securities Exchange Act of 1934, signal a significant shift in how cybersecurity is expected to be managed and reported—not merely as an IT issue but as a material business risk requiring board-level oversight, transparent strategy, and timely disclosure of incidents. The DVMS helps organizations operationalize these expectations by embedding cybersecurity directly into digital business value creation and protection architecture, transforming compliance with the SEC rules from a reactive reporting function into a strategic, performance-enhancing capability.
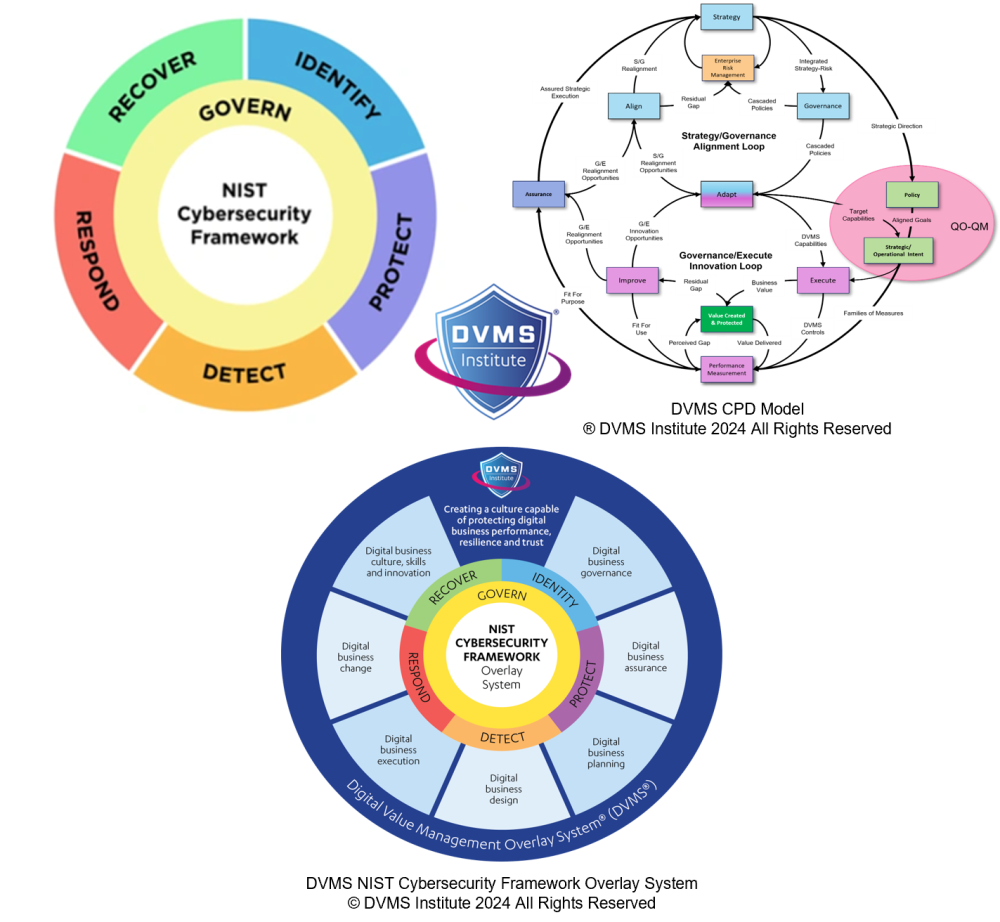
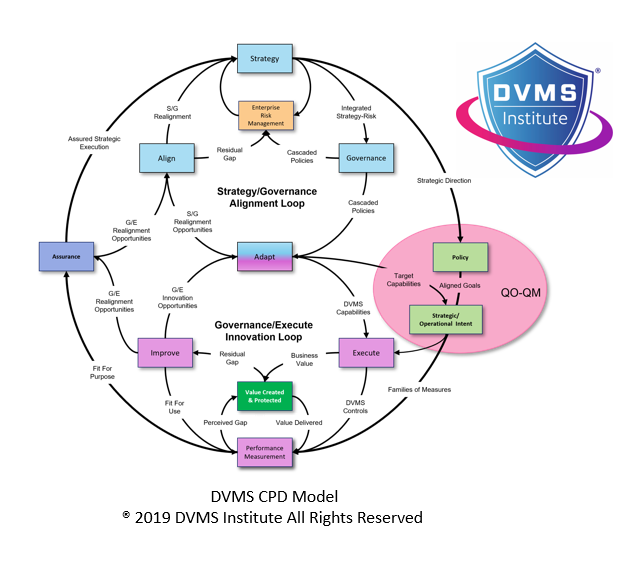
The SEC’s rules require companies to disclose their processes for assessing, identifying, and managing material cybersecurity risks, describe the role of the board and management in cybersecurity governance, and disclose material cybersecurity incidents and their impacts in a timely and standardized manner. These requirements align closely with the DVMS’s foundational concept of “strategy-risk,” which treats strategy and risk not as separate efforts but as interdependent components of a system designed to create, protect, and deliver digital business value. In the DVMS, risk is not simply something to be minimized—it is actively managed to achieve strategic outcomes. This shift in thinking is essential for public companies that must now demonstrate that cybersecurity is integral to enterprise risk management and governance.
One of the key contributions of the DVMS is its capability-based structure, notably the Z-X Model, which defines seven minimal viable capabilities that organizations must master: govern, assure, plan, design, change, execute, and innovate. These capabilities are not isolated functions but interdependent components of a system of performance and resilience. This structure provides a roadmap for how organizations can embed cybersecurity into the operational core of the business, aligning with the SEC’s expectation that risk management processes be articulated, consistently applied, and regularly evaluated. For instance, the “govern” capability ensures that cybersecurity risk is included in boardroom decision-making, with defined responsibilities and escalation paths—directly matching the SEC’s focus on governance and accountability.
The SEC’s rules also require companies to describe the board’s oversight of cybersecurity risk and management’s role in assessing and managing such risks. The DVMS equips organizations to fulfill these governance obligations by elevating cybersecurity to a strategic concern. Through structured governance processes and tools such as the Goal-Question-Metric (GQM) and Question Outcome–Question Metric (QO-QM), the DVMS helps leadership teams translate cybersecurity risks into strategic questions and measurable outcomes. These tools enable board members and executives to understand the implications of cyber risk better, evaluate the effectiveness of risk mitigation measures, and integrate cybersecurity into broader business planning and performance oversight. This fulfills not just the letter but the spirit of the SEC’s governance requirements—embedding cyber risk into the fabric of strategic oversight.
Risk management processes must also be disclosed under the SEC rules, including whether the organization has engaged third parties in these processes and how previous incidents have informed current practices. The DVMS supports this through its systems-thinking foundation, which ensures that risk management is not siloed or reactive but systemic and proactive. The CPD Model (Create–Protect–Deliver) frames risk management as a continuous process that evolves with business needs, threat landscapes, and stakeholder expectations. The model ensures that the protection of digital assets is intrinsically linked to how those assets are created and delivered, promoting a more holistic understanding of cyber risk. This aligns with the SEC’s requirement to describe how risk management processes fit into the business strategy and operations.
Incident disclosure is a major component of the SEC rules, requiring companies to report material cybersecurity incidents on Form 8-K within four business days of determining that the incident is material. The DVMS supports this by embedding incident management into the operational ecosystem, ensuring that detection, escalation, impact assessment, and response are coordinated, timely, and aligned with materiality thresholds. The DVMS FastTrack™ implementation model includes phases that progressively build an organization’s capability to respond to incidents precisely and clearly. In the early stages, companies stabilize foundational detection and response capabilities; in later phases, they integrate advanced techniques such as red-teaming and scenario-based planning. Throughout this journey, the DVMS encourages using adversarial thinking— “being the menace”—to anticipate, simulate, and prepare for threats before they materialize. This proactive posture is essential for ensuring that material incidents are detected quickly, accurately assessed, and reported within the required timeframes.
In addition to technical readiness, the SEC’s disclosure rules require companies to communicate the business impact of incidents, not just their technical details. The DVMS uniquely suits this requirement because it treats incidents as business events that disrupt digital value streams—not just technical anomalies. By integrating the 3D Knowledge Model, organizations using the DVMS can understand how incidents affect teams, collaboration pathways, and strategic alignment. This model enables a more meaningful impact analysis, helping organizations report incident consequences regarding business continuity, stakeholder impact, financial exposure, and strategic disruption—precisely the kind of material assessment required by the SEC.
Another challenge companies face in meeting the SEC’s cybersecurity rules is ensuring coherence and consistency across multiple regulatory and governance frameworks. Many public companies are already subject to requirements under SOX, NIST, ISO/IEC 27001, CMMC, and industry-specific mandates. The DVMS is designed as an overlay model, meaning it does not require abandoning existing controls or frameworks. Instead, it integrates with them, enhancing coherence, filling capability gaps, and aligning disparate processes into a unified system of governance and assurance. This allows organizations to meet SEC requirements in a way that also supports other obligations, reducing duplication and improving overall governance efficiency.
Crucially, the DVMS also addresses the cultural dimension of cybersecurity—something that is increasingly recognized as essential to sustainable risk management. The SEC rules imply, though do not explicitly mandate that cybersecurity practices be institutionalized and understood across the enterprise. The DVMS operationalizes this expectation by fostering a questioning culture, where individuals at all levels are encouraged to think critically, challenge assumptions, and participate in identifying and mitigating cyber risk. Tools like the 5 Whys and scenario-based learning exercises help embed this culture, turning compliance from a top-down enforcement model into a bottom-up, organization-wide competency.
The DVMS is particularly helpful for ensuring that cyber risk disclosures reflect continuous improvement and adaptation. One of the underlying assumptions of the SEC rules is that cyber risks are dynamic and must be reassessed regularly, considering new incidents, emerging threats, and organizational changes. The DVMS encourages a feedback-driven approach to improvement, supported by measurement systems that link operational performance to strategic outcomes. This enables companies to confidently report past incidents and how those incidents have shaped better processes, governance, and readiness for the future—an increasingly important theme in regulatory and investor scrutiny.
The DVMS offers a powerful and flexible model for helping U.S. public companies operationalize the capabilities required by the SEC’s rules on cybersecurity risk management, strategy, governance, and incident disclosure. It transforms cybersecurity from a reporting requirement into a strategic capability, enabling organizations to meet regulatory obligations while improving resilience, stakeholder trust, and business performance. By embedding governance, assurance, and continuous learning into every enterprise layer, the DVMS ensures that cybersecurity is reported and managed. For companies navigating the complexities of SEC compliance in a high-risk digital landscape, the DVMS provides a proven path to sustained assurance and adaptive value protection.
About the Author

Rick Lemieux
Co-Founder and Chief Product Officer of the DVMS Institute
The DVMS Institute teaches organizations of any size, scale, or complexity an affordable approach to mitigating cyber risk to protect digital business performance, resilience, and trust.
Rick has 40+ years of passion and experience creating solutions to give organizations a competitive edge in their service markets. In 2015, Rick was identified as one of the top five IT Entrepreneurs in the State of Rhode Island by the TECH 10 awards for developing innovative training and mentoring solutions for boards, senior executives, and operational stakeholders.
® DVMS Institute 2024 All Rights Reserved